TRAINING DAYS: 5
(4 days of training + 1 day exam)
CPD CERTIFICATION
35 Credits
EXAM DURATION
6 Hours
EXAM RETAKE POSSIBLE?
Yes. Free one more exam in 12 months
WHAT IS INCLUDED?
Training, PECB exam and certification
Training Course Overview
The Certified Lead Ethical Hacker training course enables participants to develop the competence and knowledge required to conduct ethical hacking, mainly for information systems and network penetration tests. Apart from theoretical information, the training course also includes labs that are completed with a virtual machine.
Why Should You Attend?
As the impact of security incidents in small and large organizations has increased significantly, so has the demand for ethical hacking. Ethical hacking is one of the most effective tools of safeguarding assets and protecting people and information. Ethical hacking certification is slowly becoming a standard requirement for professionals who want to work in the field of information security.
A PECB Certified Lead Ethical Hacker certification will help you demonstrate your ability to lawfully assess the security of systems and discover their vulnerabilities. The training course provides information on the latest ethical hacking methods and tools. It also provides a methodology for conducting penetration tests in accordance with standards and best practices, such as the Penetration Testing Execution Standard (PTES) and the Open Source Security Testing Methodology (OSSTMM).
Understanding hackers’ strategies helps solve security issues and challenges. After attending the training course, you will be able to plan, manage, and perform information security penetration tests.
The PECB Certified Lead Ethical Hacker training course is based on the concept of practicing what you learned. It includes lab sessions and practical examples to help you apply the theory into practice.
The training course is followed by an exam. If you pass, you can apply for a “PECB Certified Lead Ethical Hacker” credential. For more information about the examination process, please refer to the Examination, Certification, and General Information section below.
Who Can Attend?
Learning objectives
This training course will help you:
Educational approach
Prerequisites
The main requirement for participating in this training course is having knowledge of information security concepts and principles and advanced skills in operating systems. It is recommended for participants to have knowledge of computer networks and the concepts of programming.
Course Agenda
Day 1: Introduction to ethical hacking
Day 2: Initiating the reconnaissance phase
Day 3: Initiating the exploitation phase
Day 4: Post-exploitation and reporting
Day 5: Certification exam
Examination
The “PECB Certified Lead Ethical Hacker” exam meets all the requirements of the PECB Examination and Certification Program (ECP). It covers the following competency domains:
Domain 1: Information gathering tools and techniques
Domain 2: Threat modeling and vulnerability identification
Domain 3: Exploitation techniques
Domain 4: Privilege escalation
Domain 5: Pivoting and file transfers
Domain 6: Reporting
The PECB Certified Lead Ethical Hacker exam comprises two parts: practical exam and report writing. The practical exam requires the candidate to compromise at least two target machines through penetration testing. The process should be documented in a written report. The PECB Certified Lead Ethical Hacker exam is an open book exam. Candidates are allowed to use training course materials and personal notes during the examination process.
General Information
1. Participants will be provided with training course material containing over 450 pages of information, practical examples, and exercises.
2. An attestation of course completion worth 35 CPD (Continuing Professional Development) credits will be issued to the participants who have attended the training course.
3. Candidates who have completed the training course but failed the exam are eligible to retake it once for free within a 12-month period from the initial date of the exam.
Certification
Upon the successful completion of the exam, you can apply for the “PECB Certified Lead Ethical Hacker” credential, depending on your level of experience, as shown in the table below. You will receive the certificate once you comply with all the relevant educational and professional requirements.
The requirements for Lead Ethical Hacker certification is as follows:
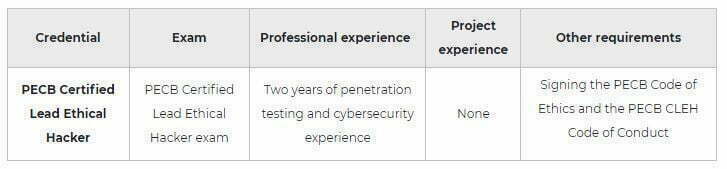
To be considered valid, the penetration testing and cybersecurity experience should include the following:
1. Determining the scope of ethical hacking
2. Defining a penetration testing approach
3. Performing the steps that should be followed during a penetration testing
4. Defining the penetration testing criteria
5. Evaluating penetration test scenarios and treatment options
6. Using the methods that help increase the security of operation systems
7. Reporting the penetration testing results